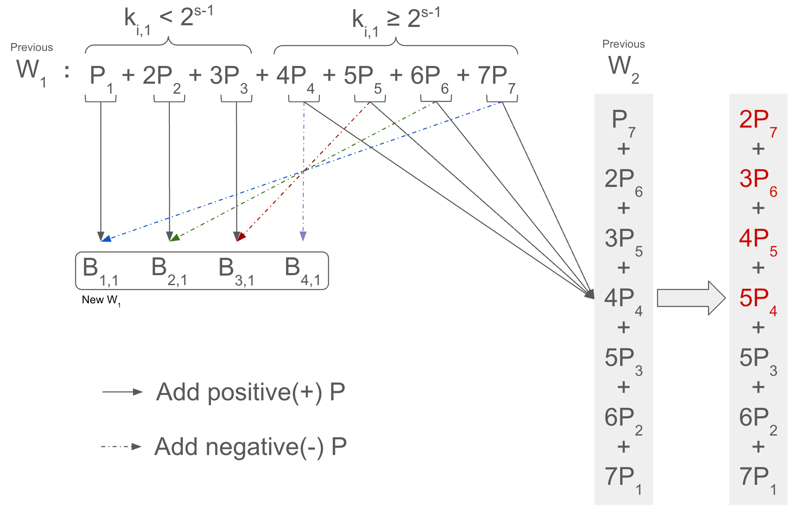
Stage 1: Separating previous window W_1 into new buckets
Stage 1: Separating previous window W_1 into new buckets

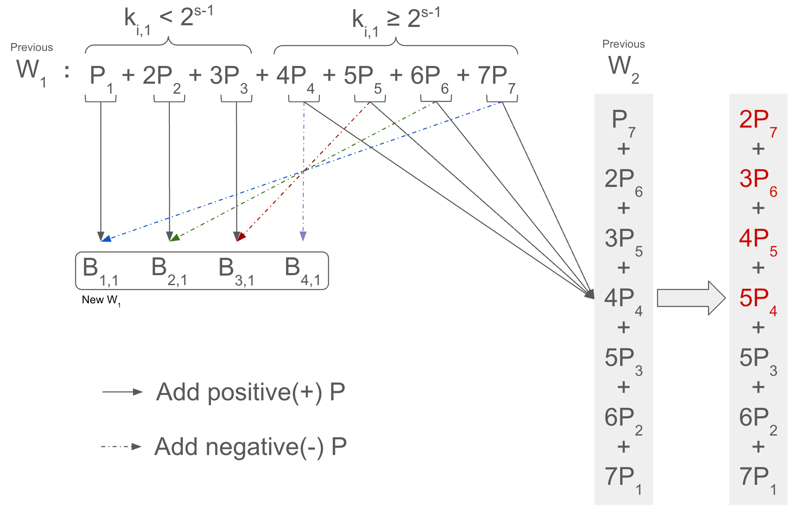
Stage 2: Separating previous window W_2 into new buckets
void FillDigits(uint32_t kLambda, uint32_t s, const ScalarField& f, std::vector<int64_t>* digits) {
// The size of `digits` must be equal to ceil(lambda / s)
// (lambda: total number of bits, s: window size in bits)
CHECK_EQ(digits->size(), static_cast<size_t>(std::ceil(kLambda / s)));
// `radix` is 2^s — the maximum range per window
uint64_t radix = uint64_t{1} << s;
// `carry` to be propagated to the next window
uint64_t carry = 0;
size_t bit_offset = 0;
for (size_t i = 0; i < digits->size(); ++i) {
// mᵢ: s-bit value extracted from the current window, including previous carry
uint64_t m_i = f.ExtractBits(bit_offset, s) + carry;
// Compute carry: if mᵢ is greater than or equal to radix / 2, carry = 1;
//. otherwise carry = 0
// This is based on the NAF rounding threshold (radix / 2)
carry = (m_i + (radix >> 1)) >> s;
// Convert mᵢ to its NAF form: mᵢ - carry * 2^s
(*digits)[i] = static_cast<int64_t>(m_i) - static_cast<int64_t>(carry << s);
bit_offset += s;
}
// Apply the final carry to the last digit
// This adjustment preserves the total scalar value
digits->back() += (carry << s);
}
void AddBasesToBuckets(uint32_t s, const std::vector<Point> bases,
const std::vector<std::vector<int64_t>>& digits,
size_t window_index, std::vector<Bucket>& buckets) {
for (size_t i = 0; i < scalar_digits.size(); ++i) {
int64_t scalar = scalar_digits[i][window_index];
if (0 < scalar) {
// If the scalar is positive:
// Place the corresponding base into the (scalar - 1)-th bucket
//
// Why `scalar - 1`?
// Because scalars range from 1 to 2^{s-1} - 1 in NAF,
// but bucket indices are 0-based (0 to 2^{s-1} - 2)
// so we subtract 1 to get the correct index.
buckets[static_cast<uint64_t>(scalar - 1)] += bases[i];
} else if (0 > scalar) {
// If the scalar is negative:
// Place the *negated* base into the (-scalar - 1)-th bucket
//
// Why `-scalar - 1`?
// Because negative scalars range from -1 to -2^{s-1},
// and we want to map -1 → index 0, -2 → index 1, ..., just like for positives.
buckets[static_cast<uint64_t>(-scalar - 1)] -= bases[i];
}
}
}