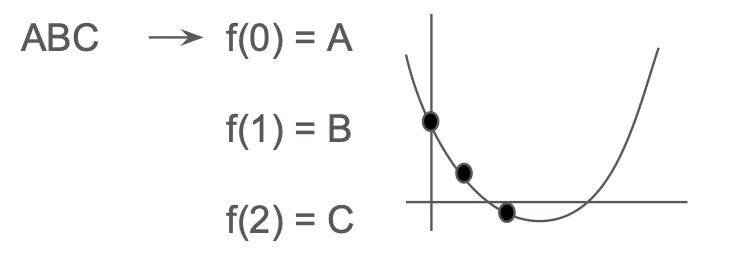
Figure 1. Reed Solomon Encoding — Converting a message into a polynomial
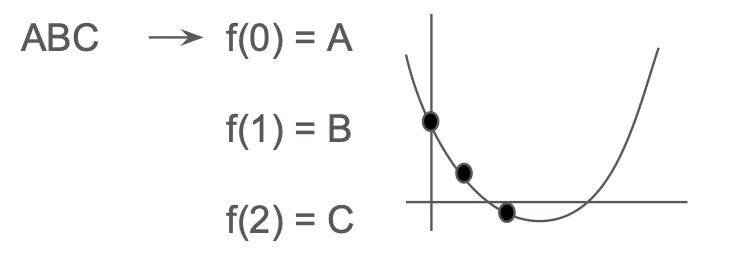
Figure 1. Reed Solomon Encoding — Converting a message into a polynomial
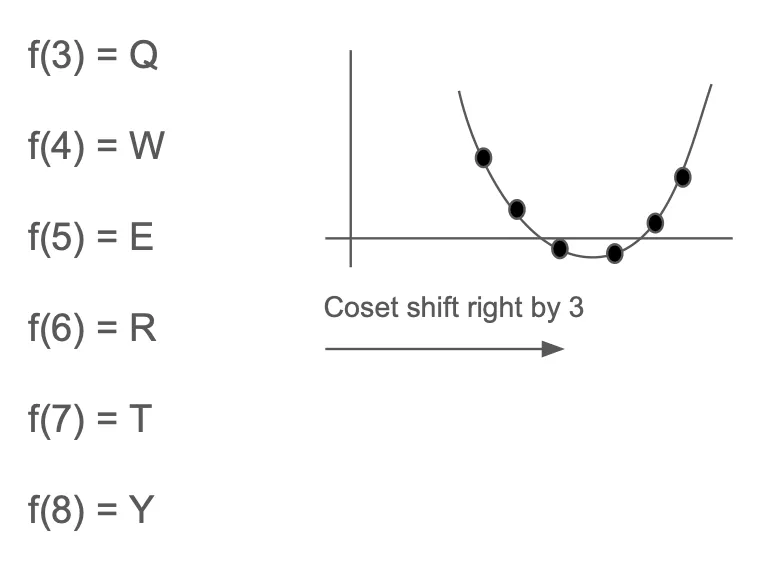
Figure 2. Reed Solomon Encoding — Extrapolating the polynomial into a larger codeword.

Figure 3. Reed Solomon Encoding — Checking a faulty value in a codeword.

Figure 4. Resulting Merkle Tree from the example evaluations of the original polynomial
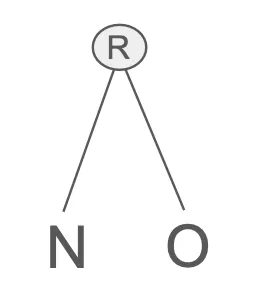
Figure 5: Resulting Merkle Tree from the example’s first folded polynomial evaluations
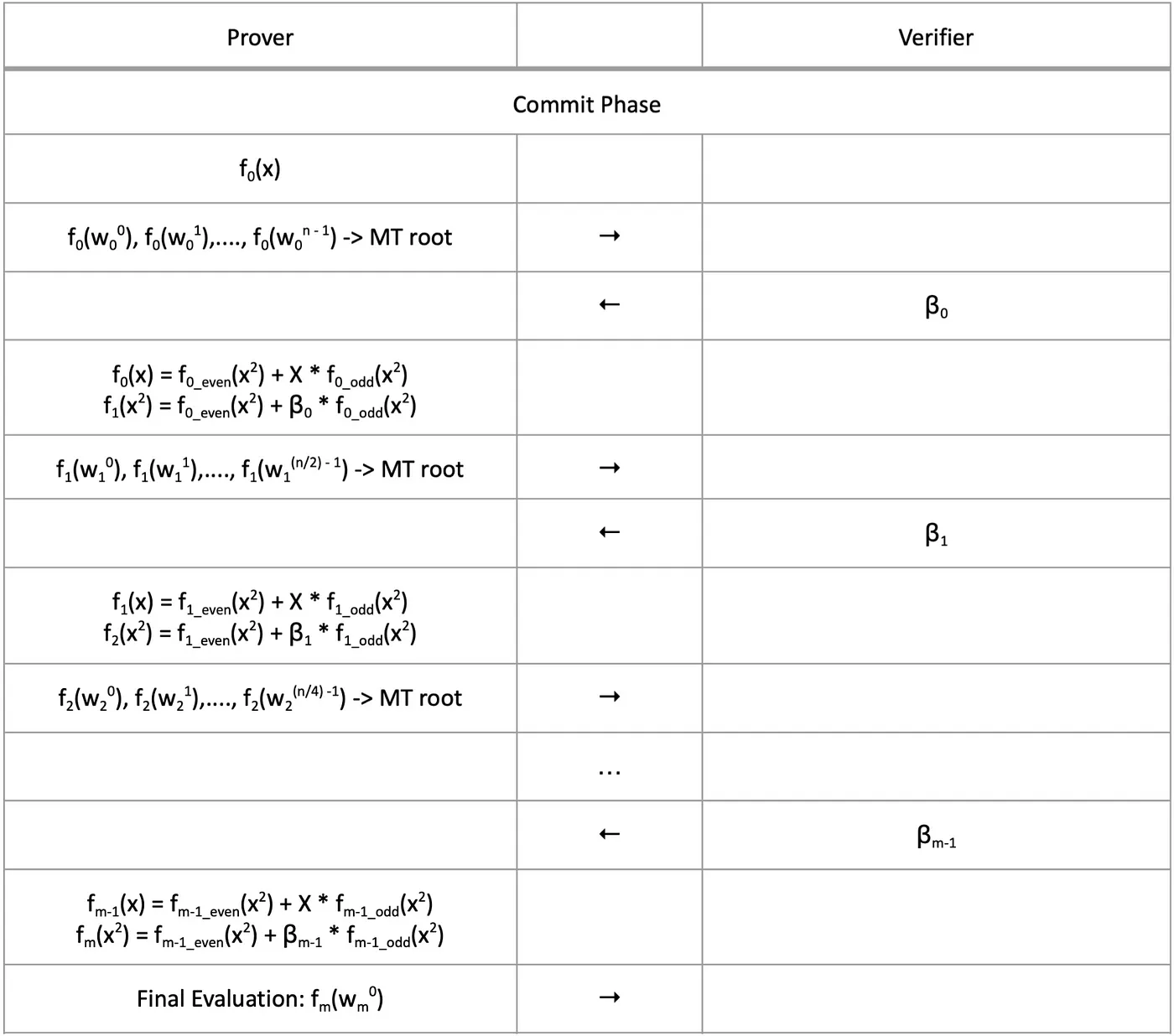
Figure 6. The Commit Phase of the FRI protocol illustrated in a table, where n = domain size and m = the total number of folding rounds aka ⌈log(d)⌉ with d being the maximum degree
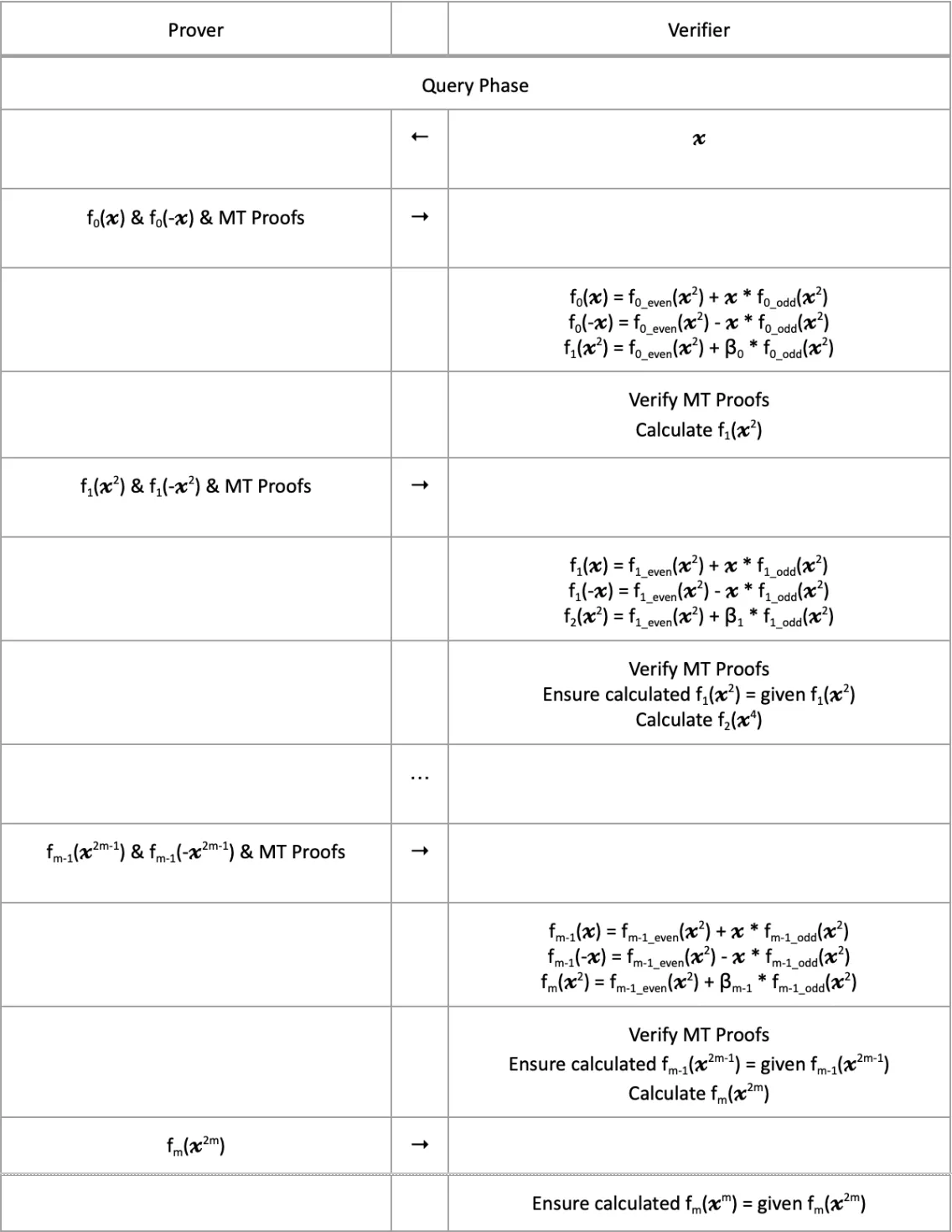
Figure 7. A single query of the Query Phase illustrated in a table, where n = domain size and m = the total number of folding rounds aka ⌈log(d)⌉ with d being the maximum degree